
Welcome to the Self-Realization Fellowship
Online Meditation Center
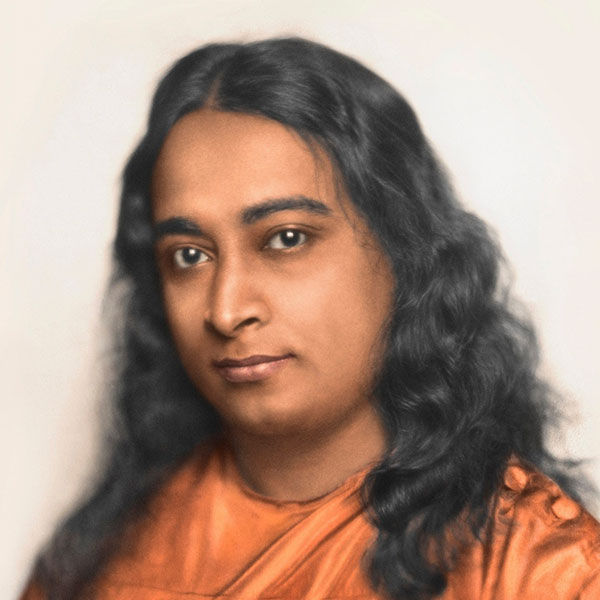
“Group meditation is a castle that protects the new spiritual aspirants as well as the veteran meditators. Meditating together increases the degree of Self-realization of each member of the group by the law of invisible vibratory exchange of group magnetism.”
– Paramahansa Yogananda
SRF/YSS President Brother Chidananda introducing the SRF Online Meditation Center at the 2019 Convocation
Welcome
In the spirit of our revered guru and founder, Paramahansa Yogananda, I joyfully welcome you to the Self-Realization Fellowship Online Meditation Center. As with all SRF centers and meditation groups, this online venue is overseen by the monastics in Center Department at our International Headquarters, and run with the help of a managing council of lay member volunteers. (Read More)
Through this online center, we look forward to sharing with you the blessings of experiencing group meditation and study of Paramahansaji’s teachings, in fellowship with many other SRF members and friends from around the world.
In divine friendship,
Brother Chidananda
President, Self-Realization Fellowship/Yogoda Satsanga Society of India
Sign up to receive updates and program announcements.
Why an Online Meditation Center?
There are many tangible and intangible benefits to participating physically at a Self-Realization Fellowship temple, center, or meditation group, and we encourage everyone to attend in person if this is possible for them. However, many members of our worldwide spiritual family live far from a Self-Realization group or center – or are unable for other reasons to attend in person. Now all devotees, regardless of their location or circumstances, have the opportunity to join together in spiritual fellowship with other truth-seeking souls for group meditation and spiritual study.
Online Group Meditations
Throughout his life, Paramahansa Yogananda described group meditation as invaluable for deepening one’s practice. Now you’ll have the opportunity to join group meditations regardless of your location or circumstances.
By participating in an online group meditation, you will join followers of Paramahansa Yogananda in meditations that are happening around the world. No matter where you live, you’re likely to find a meditation that fits your schedule.

Online Study Groups
Paramahansa Yogananda’s teachings present in-depth wisdom on a vast range of inspiring and universal truths.
In the same way that group meditation reinforces the effort of every member of the group, studying the guru’s teachings in a group helps each member to deepen their focus and concentration on these timeless truths.
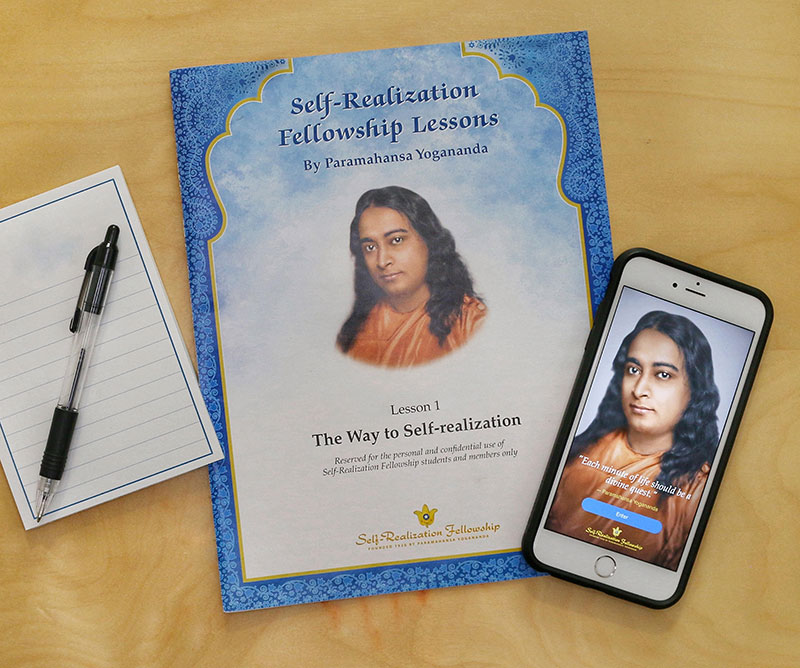
Participate in group study of the Self-Realization Fellowship Lessons, Paramahansa Yogananda’s spiritual classic, Autobiography of a Yogi, and his commentaries on the Bhagavad Gita (God Talks with Arjuna) and the teachings of Jesus in the Gospels (The Second Coming of Christ: The Resurrection of the Christ Within You).
“It was amazing how the vibration of Master was manifest in my online meditation and the lessons group more potently than just meditating or studying by myself.”
See the Calendar of Services

How to Participate
Experiences shared with us
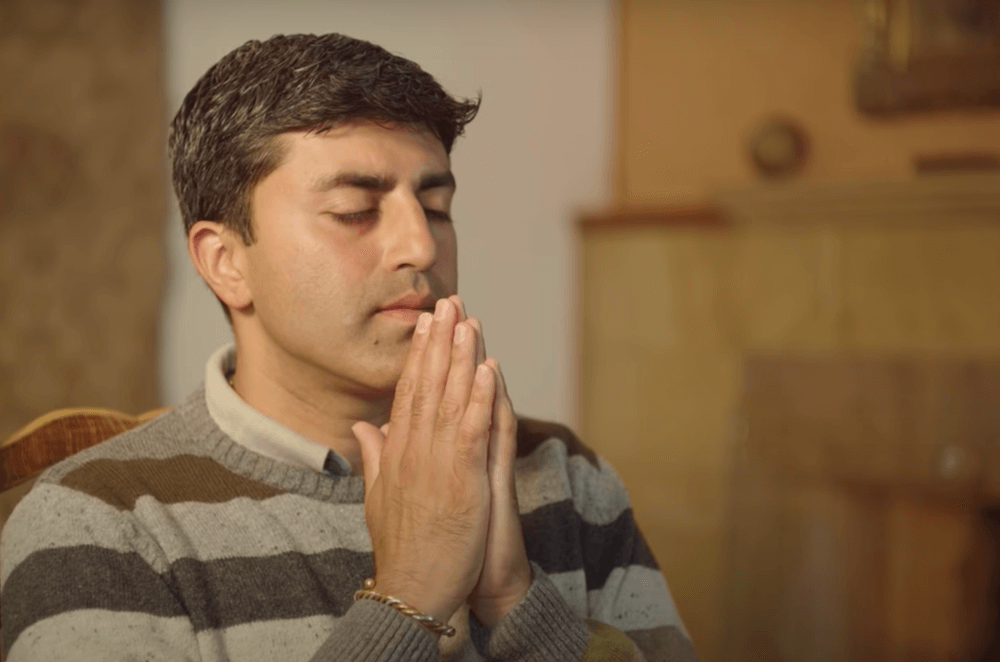
“It truly captured the spirit of a group meditation. It was wonderful. I was surprised how similar it was to an in-person group meditation!”
“I had a great experience with our online meditation. It really does feel like we’re part of a group!”
“It was such a nice feeling being able to wake up early and sit with devotees to meditate and hear live kirtan!”
“It’s amazing how much it feels like a real group meditation.”
“I really enjoyed it. I could feel the strength and connection of the group.”
New to Meditation?
Watch this video to get started with basic instructions on how to meditate.
We also invite you to learn more about the powerful system of meditation techniques at the very core of Paramahansa Yogananda’s teachings: the Kriya Yoga science of meditation. Know more about these techniques in the comprehensive series of SRF/YSS Lessons.
